Why IGA Migration Should Start Before You Choose the IGA
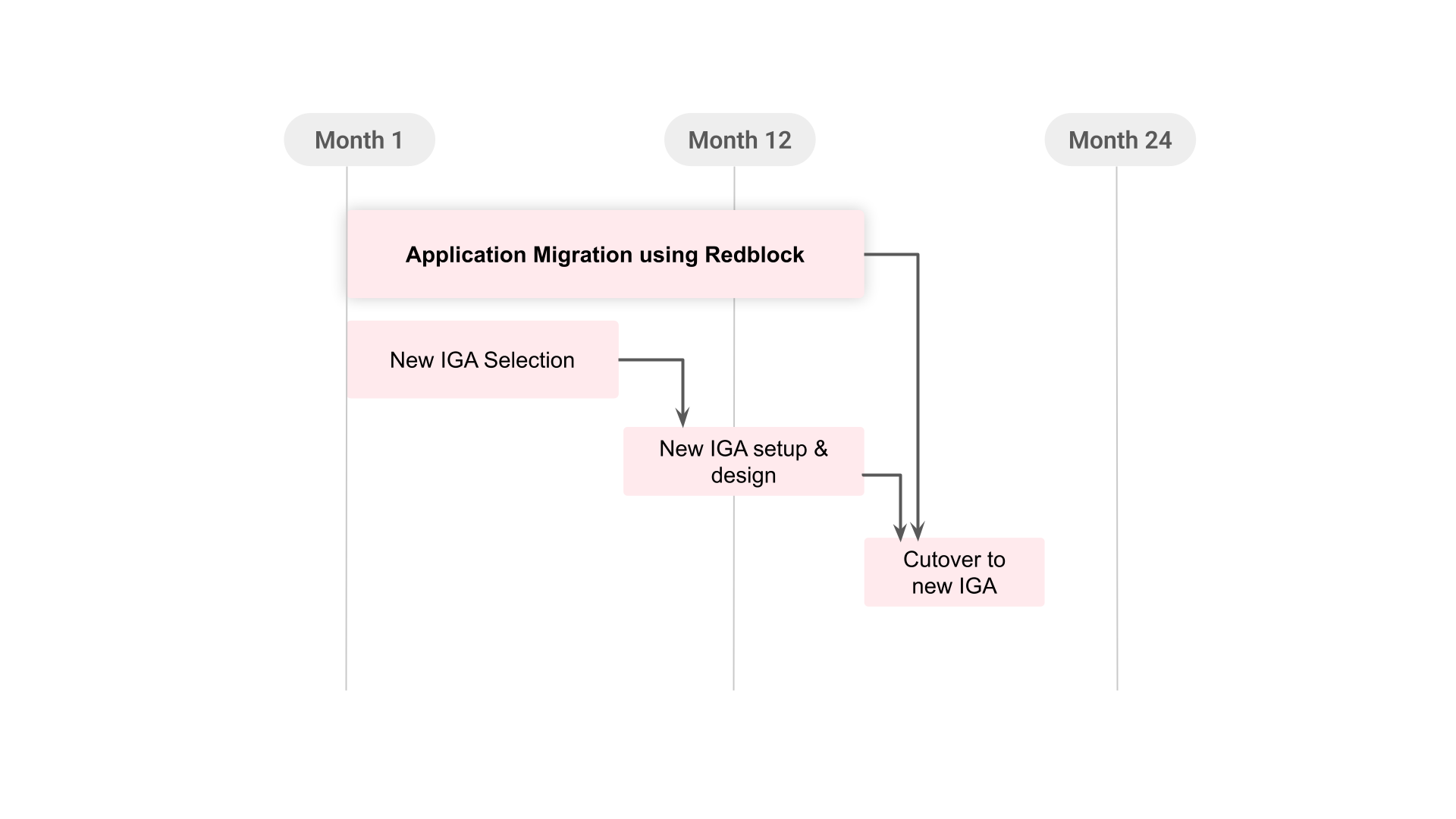
Table of Contents
Most Identity Governance and Administration (IGA) migrations fail because they start in the wrong place.
Enterprises typically follow the same, logical sequence: choose a platform, define the architecture, configure the environment, and then finally start onboarding applications. This approach is intuitive, but it is the primary reason IGA rollouts drag on for years.
1. The Hidden Critical Path in IGA Migration
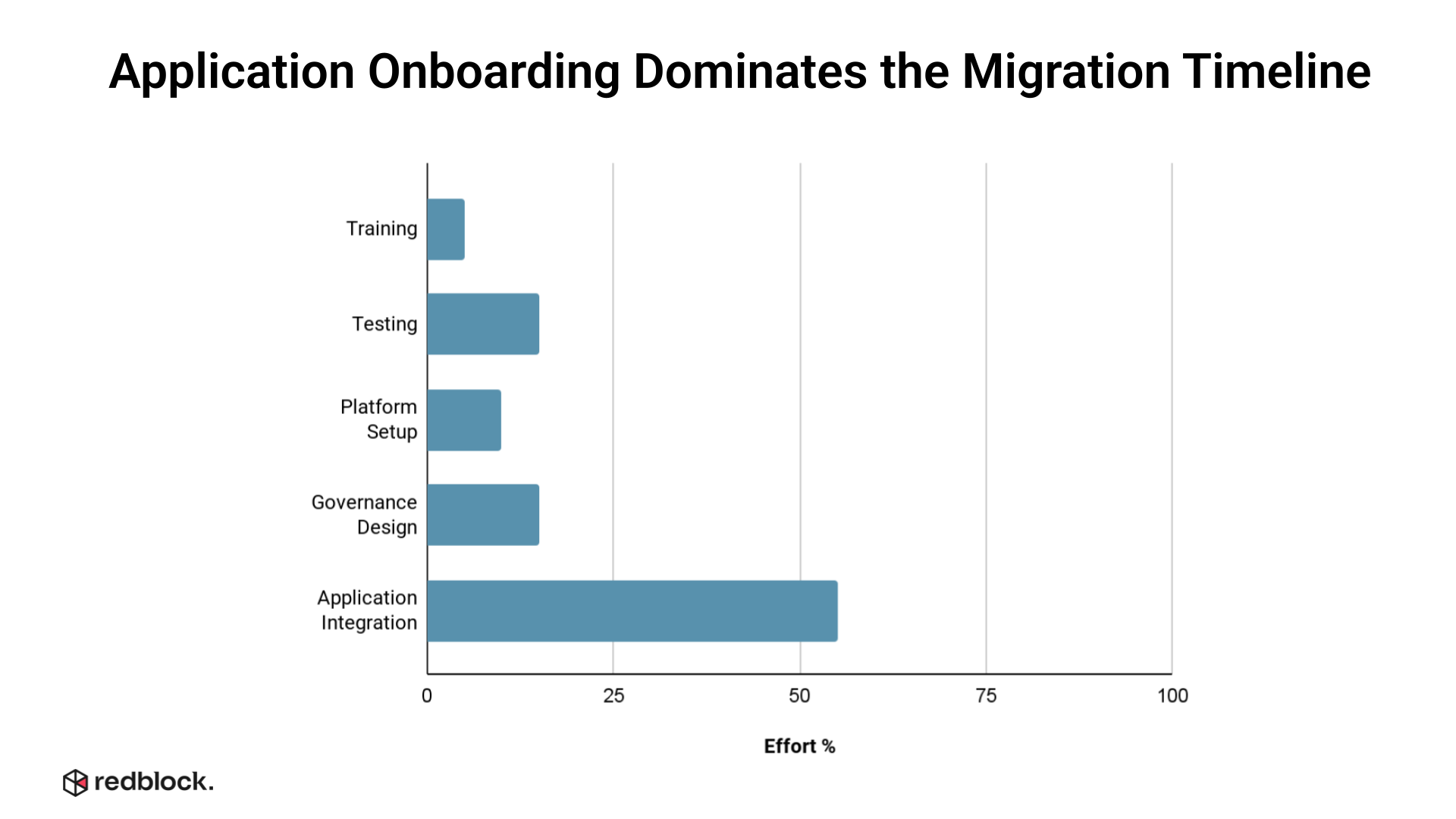
Most IGA migration plans allocate time to vendor selection, governance design, configuration, testing, deployment, and application onboarding.
But in practice, application onboarding often dominates the timeline.
That is because application integration is not one task. It is many tasks bundled together:
- Identifying the right application owner
- Understanding how accounts are represented
- Mapping roles, groups, and entitlements
- Cleaning stale, duplicate, or orphaned accounts
- Determining whether APIs or connectors exist
- Building workflows for applications without clean integration paths
- Validating access changes inside each application
- Producing evidence for audit and compliance teams
Each application introduces its own identity model. Some applications expose mature APIs. Some only support CSV exports. Some have admin consoles with no programmatic interface. Some have local roles that do not map cleanly to enterprise policy. Some have entitlement names that only one business owner understands.
This is why application onboarding becomes the hidden critical path.
The core problem is sequencing.
Traditional IGA migrations often delay application-level discovery until after the new platform is selected. That means the enterprise discovers the hardest integration problems late, when timelines are committed and expectations are locked.
By then, the migration plan starts to bend around reality.
2. More Applications Means More Migration Risk
The migration risk rises sharply as the application estate grows.
An enterprise migrating 25 applications has one type of program. An enterprise migrating 250 applications has a very different one..
Every additional application can introduce a different account model, data quality issue, entitlement structure, API limitation, workflow exception, or remediation process. As the number of applications increases, the timeline does not always grow linearly. Complexity compounds.
A small number of well connected applications can create the impression that the migration is under control. But the real challenge usually appears when the program expands beyond the first set of priority systems. That is where coverage slows down.
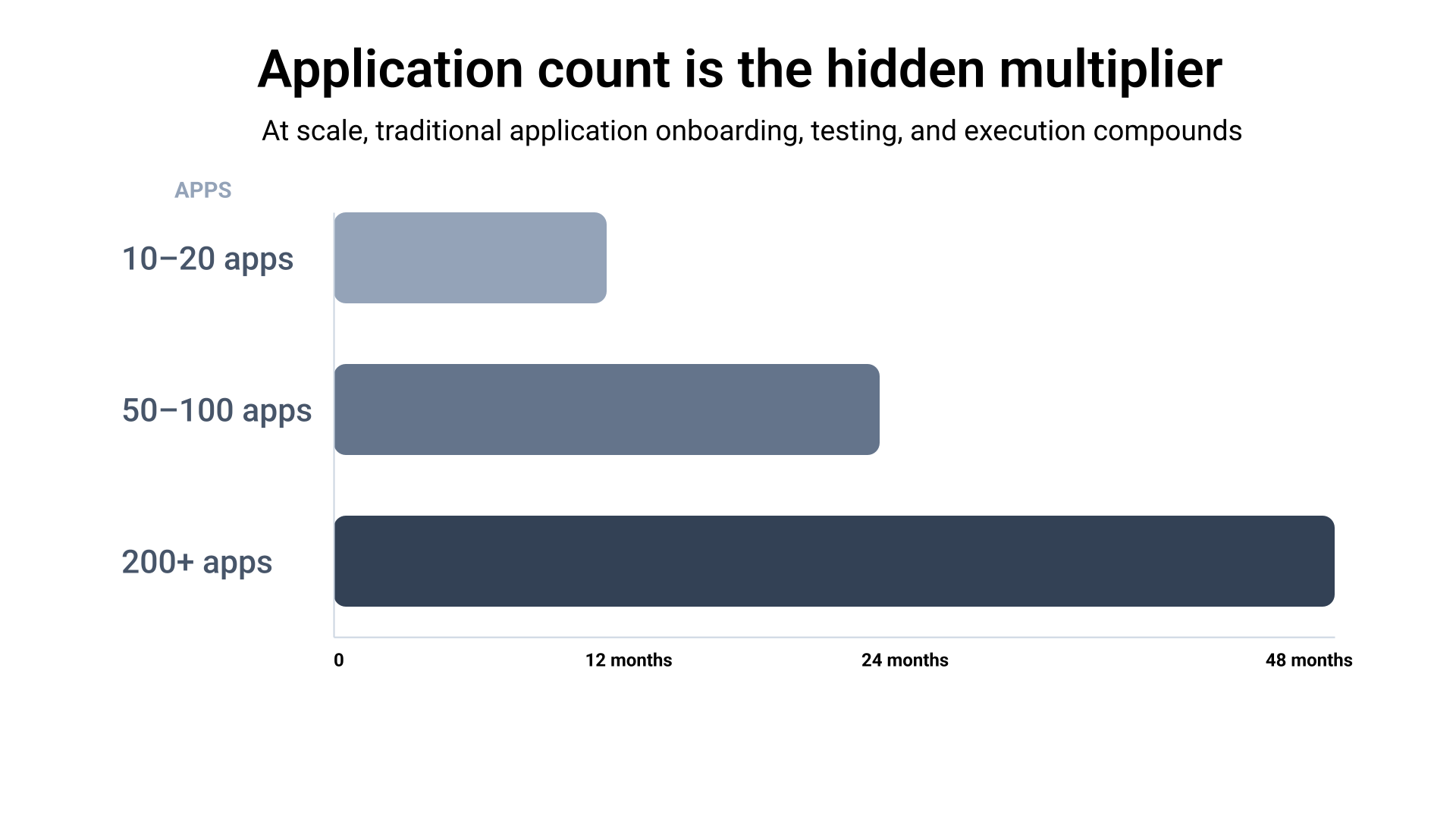
This is also why many IGA programs make strong early progress and then slow down dramatically.
The first wave of applications is usually familiar, important, and better supported. The later waves are messier. They include departmental tools, regional systems, legacy applications, SaaS products with limited APIs, and business critical systems that were never designed for modern identity governance.
These applications still carry identity risk. They still have users, privileges, stale access, local administrators, and audit obligations. But they are often the applications that get pushed later in the migration.
3. The Traditional Sequence Creates Late Surprises
In a traditional IGA migration, application complexity is discovered after several major decisions have already been made.
A typical sequence looks like this:
- Select the IGA platform
- Define the governance model
- Configure the new IGA environment
- Begin application discovery
- Identify connector gaps
- Normalize application data
- Build manual or custom workflows
- Remediate access issues
- Validate outcomes
- Produce audit evidence
This sequence creates a structural problem. The application estate is where the uncertainty lives, but it is often addressed after the platform work has started.
Consequently, organizations often remain unaware of which applications are manageable, which present significant integration challenges, which necessitate workflow automation, or which require extensive data remediation until the migration process is already in progress.
At this juncture, project teams are frequently forced to make suboptimal strategic compromises:
- A reduction in the overall scope of the project.
- The extension of established project timelines.
- An increased reliance on manual operational processes.
- The prioritization of only those applications that offer the least complex integration paths.
None of these alternatives represent a successful migration outcome.
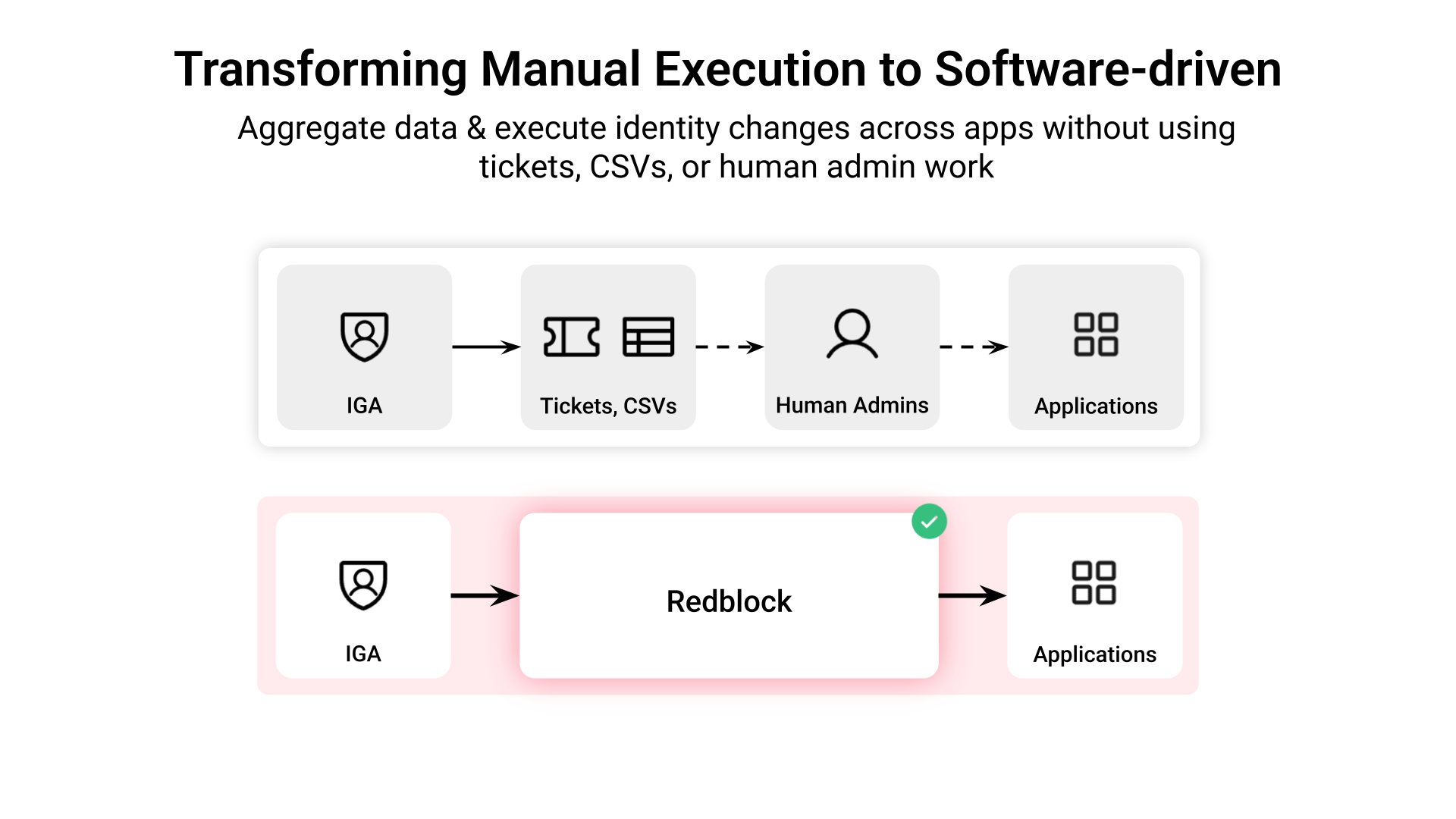
A subset of applications may have mature connectors, but many applications still sit outside full governance coverage. These applications are often managed through manual processes, tickets, or local administrators. This creates a critical governance and enforcement gap: if a governance decision is made, but the downstream application is not updated reliably, the control is incomplete.
An IGA migration's goal shouldn't be swapping out governance screens. It should be improving identity coverage, reducing control gaps, and creating reliable enforcement across the enterprise application estate.
That requires starting where the work actually lives.
4. Redblock’s Application-First Approach to IGA Migration
Redblock enables a different model: Application-First IGA Migration.
Instead of waiting for the final IGA platform decision, Redblock can begin preparing the application estate earlier in the program.
This includes:
i. Data Readiness and Visibility
Redblock pulls and maps account data and entitlement structures from all applications, even those without clean APIs. This cleans up identity data early, giving your team immediate, accurate visibility into access risks before the platform migration even starts.
ii. Automated Execution Workflows
For legacy and disconnected systems, Redblock builds the automated execution paths needed for common actions like deprovisioning. This means governance decisions are instantly and reliably enforced at the application level, even without traditional connectors.
iii. Verification and Audit Compliance
Redblock validates every identity action, recording the actions and verifying the final application state. This creates automated evidence that gives audit and compliance teams reliable proof of enforcement.
Together, these capabilities allow enterprises to achieve application readiness before the IGA migration reaches the execution phase.
The IGA still remains the governance system of record. It remains the control plane for policies, certifications, approvals, and access decisions. Redblock operates at the execution layer, serving as the bridge where policies become reality. While the IGA decides, Redblock prepares, executes, verifies, and provides evidence at the application level.
5. Running the Migration in Parallel
A better migration sequence separates two workstreams that are often unnecessarily serialized.
1. The first workstream is IGA selection and configuration.
2. The second workstream is application readiness.
In the traditional model, the second workstream waits for the first. With Redblock, both can run in parallel.
While the enterprise evaluates IGA vendors, Redblock can begin analyzing priority applications. While the IGA architecture is being finalized, Redblock can aggregate accounts and map entitlements. While the new IGA platform is being configured, Redblock can prepare application-specific execution workflows.
In some cases, this application work can begin before the new IGA vendor is selected.
That matters because the application estate does not become less complex while the enterprise is making a platform decision. All the underlying complexity, including the accounts, entitlements, and stale access, exists regardless of the platform decision.
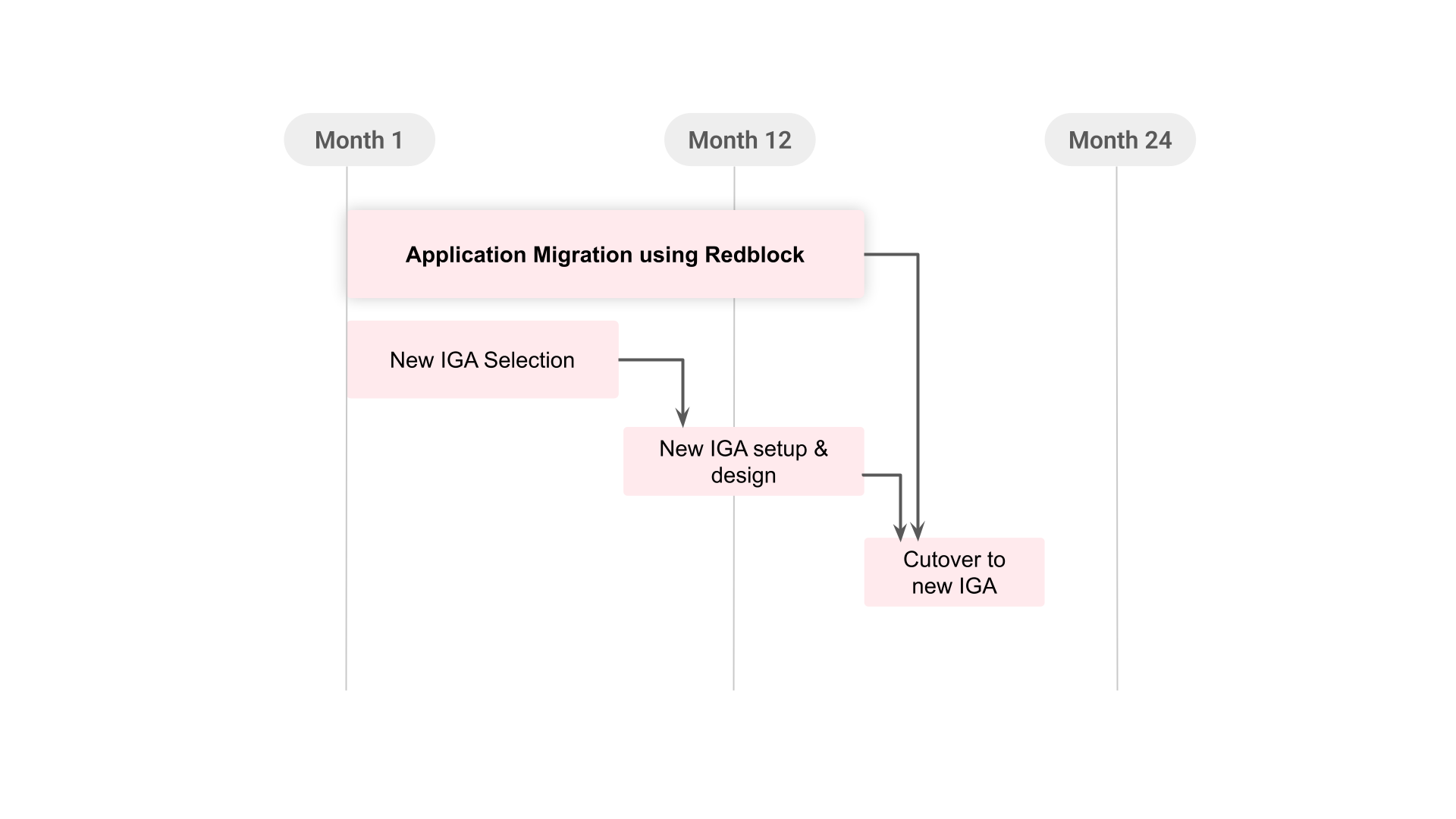
This parallel model reduces the risk of late surprises.
By the time the new IGA platform is selected, the enterprise can already have a clearer view of application complexity, data quality, entitlement structures, and execution requirements.
Instead of starting application onboarding from zero, the team starts with prepared application intelligence and reusable execution paths.
6. Why This Matters for CIOs, CISOs, and Identity Teams
Starting application integration earlier changes the risk profile of an IGA migration.
It helps teams identify difficult applications sooner. It reduces the chance that connector gaps appear late in the program. It gives implementation teams cleaner application data. It creates a clearer view of access risk before the new IGA platform is live. It gives audit and compliance teams better evidence of what is actually happening inside applications.
Most importantly, it gives the enterprise a faster path to coverage.
For CIOs, this can reduce migration uncertainty and implementation drag.
For CISOs, it can reduce the period where applications remain outside reliable governance and enforcement.
For identity teams, it can reduce the manual burden of collecting data, mapping entitlements, and chasing remediation through tickets and spreadsheets.
The outcome goes beyond merely accelerating the timeline; it facilitates a migration that is significantly more manageable.
7. Conclusion: A Better Starting Point for IGA Modernization
The longest, hardest, and least predictable part of any IGA program is not the platform, but the application estate underneath it. The traditional, sequential approach guarantees that this complexity is only discovered late in the timeline, increasing risk and forcing difficult tradeoffs. Redblock shifts the starting point. By enabling the application readiness work to run in parallel with IGA selection and configuration, enterprises gain earlier visibility, reduce late-stage surprises, and accelerate their path to full governance coverage. The goal is a better-controlled migration, achieved by starting where the work actually lives: the applications.
Close Your IAM Blast Radius.
See how Redblock replaces ticket-driven identity execution with continuous lifecycle enforcement across your application estate.