Tickets and CSVs
Are Not Identity Enforcement.
Tickets and CSVs Are Not Identity Enforcement.
Redblock's Agentic AI replaces tickets and CSVs with continuous, verified execution across disconnected applications.
Works with Industry leading Identity Platforms




















Beyond Batch IAM
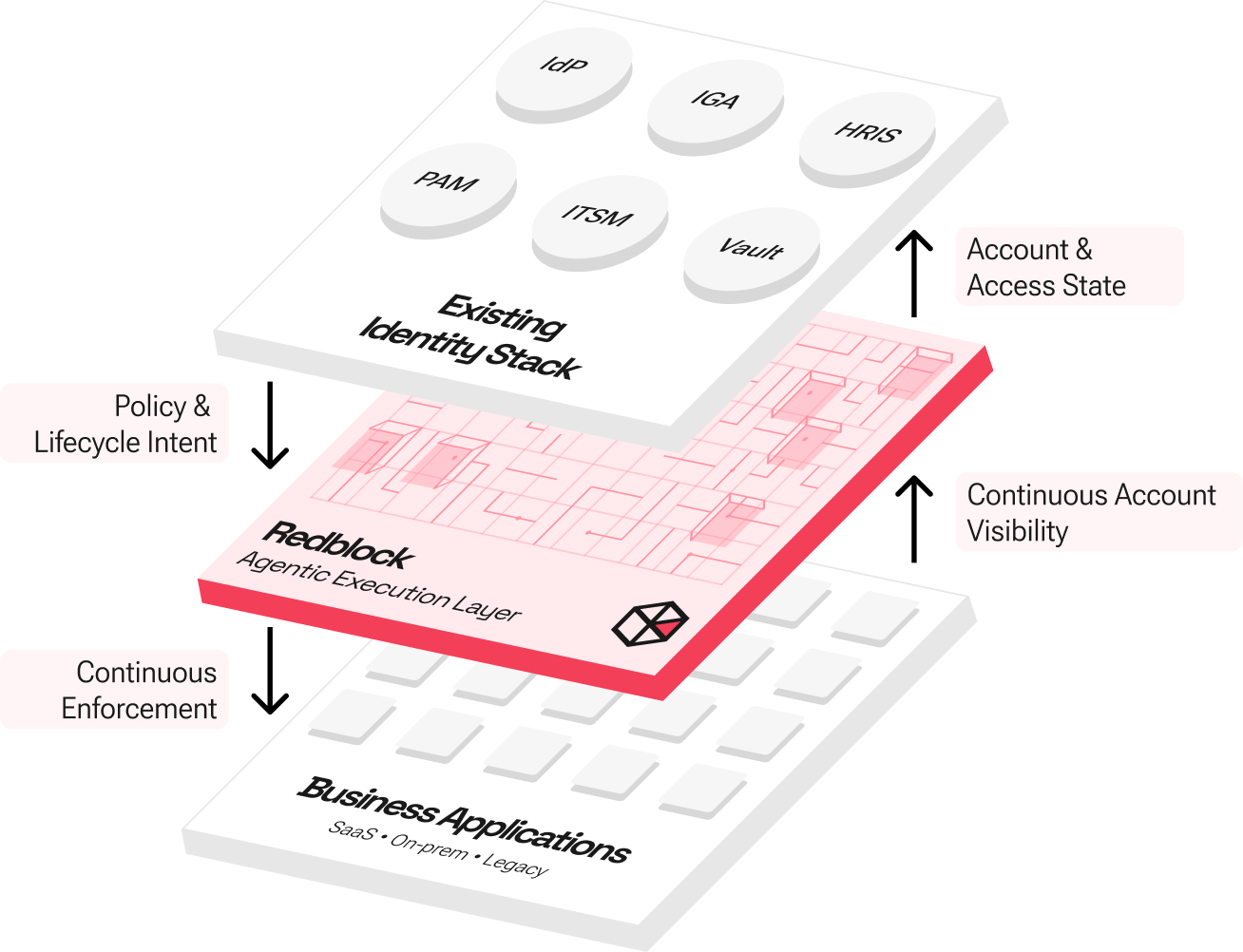
Your IAM Stack
Lacks 100% App Coverage.
It Needs a Way to Reach the Rest.
Your IAM Stack Lacks 100% App Coverage. It Needs a Way to Reach the Rest.
Traditional IAM only works where integrations exist. Redblock’s Agentic AI brings disconnected apps into your existing Identity stack.
Enforce Lifecycle Changes Everywhere
Automatically execute JML updates inside business applications as identity status changes — without tickets, scripts, or manual follow-ups, so orphan accounts don’t linger between review cycles.
Continuously Aggregate Accounts and Entitlements
Replace ticket-driven reconciliation with continuous, on-demand aggregation of users, roles, and access across disconnected and hard-to-manage applications—reducing entitlement drift as it emerges.
Replace Manual Identity Enforcement
Eliminate spreadsheets and ITSM workflows from day-to-day identity operations. Redblock carries out IAM decisions directly inside applications — reducing delayed revocations and human-dependent access gaps.
USE CASE SPOTLIGHT
Remove Access Instantly
Across Disconnected Applications.
Scenario: A leaver event occurs–and access must be removed across applications that don’t integrate with IAM.


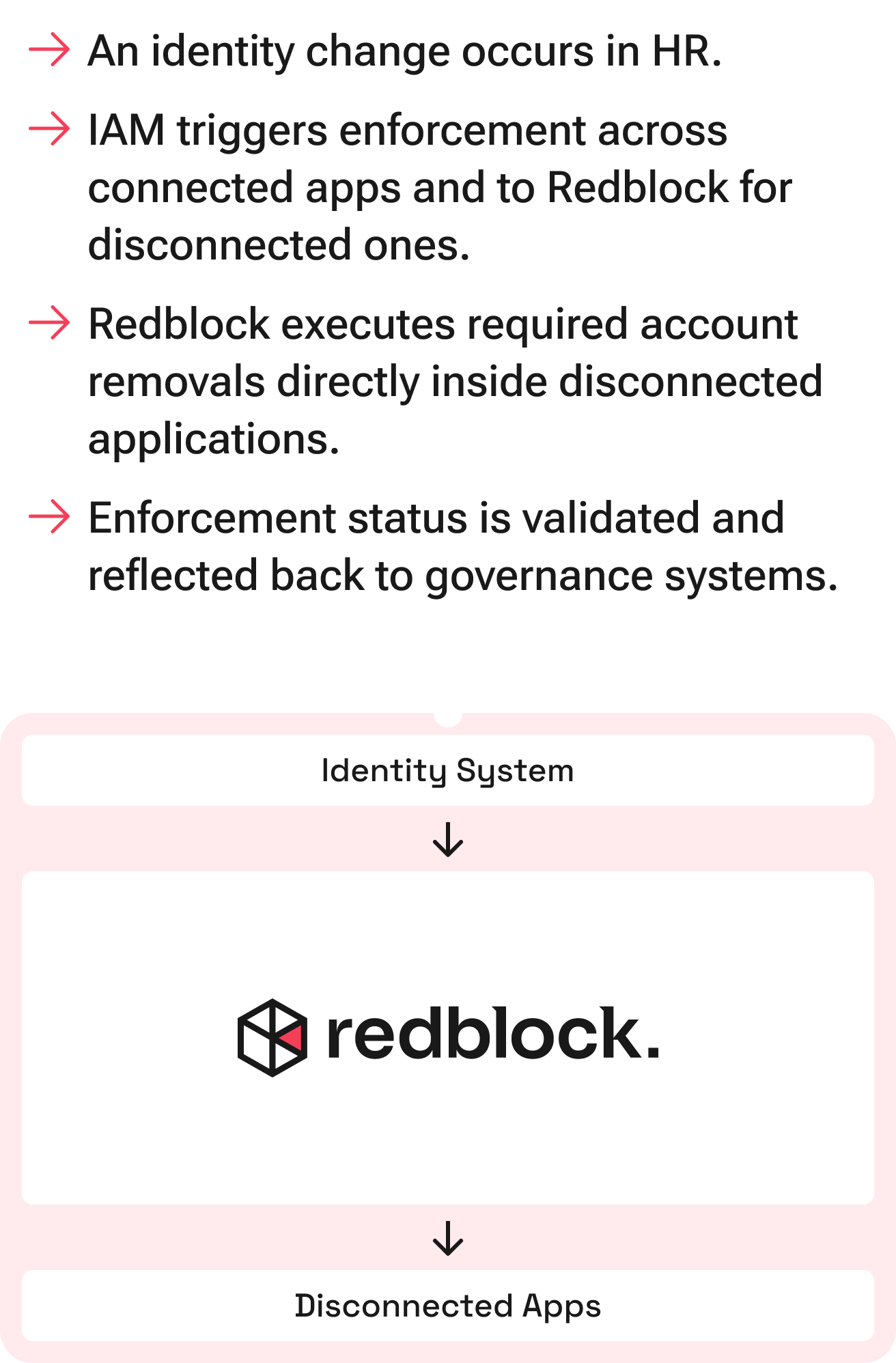
Common use cases
Secure the 80–90% of Apps
Outside Your IAM Blast Radius.
Secure the 80–90% of Apps Outside Your IAM Blast Radius.
Continuously Aggregate Users and Entitlements
Bring the 80–90% of business apps into your identity visibility plane with on-demand aggregation of accounts, roles, and access.
Eliminate Orphan Accounts and Entitlement Creep
Detect and remove stale accounts and forgotten privileges before they become breach paths — not just during quarterly reviews.
Accelerate Enforcement Without Connector Programs
Onboard and enforce identity controls across new or legacy applications without multi-year integration projects.
Enterprise Ready by Design
Secure, Auditable Identity Enforcement
Redblock extends your IAM stack with continuous enforcement — without compromising security, auditability, or control.
Least-Privilege by Default
Redblock operates with scoped access and full activity logging inside enforced applications.
Continuous Audit Evidence
Every lifecycle action and entitlement update is recorded and reconciled back to governance systems.
Designed to Extend, Not Replace
Redblock works alongside your IGA, IdP, PAM, ITSM, and Vault systems — preserving existing investments while closing enforcement gaps.
Flexible Deployment Models
Cloud or isolated deployments aligned to enterprise security and compliance requirements.
How Redblock works
Purpose-Built Identity Execution. Powered by Agentic AI.
Redblock uses purpose-built agentic automation to execute identity decisions inside business applications with strict guardrails, deterministic controls, and full auditability.
Guardrailed, Identity-Scoped Agents
Redblock agents operate within defined identity boundaries, purpose-built for lifecycle enforcement, not general-purpose automation.

No open-ended autonomy

No unrestricted task execution

Scoped strictly to identity actions
AI-Assisted, Policy-Driven Execution
AI translates identity intent into application-specific actions, but enforcement remains bound to governance rules and deterministic workflows.

Policy remains the source of truth

Algorithms and controls govern execution

AI assists, it does not decide
Deterministic and Verifiable Outcomes
Every action is executed with validation, logging, and reconciliation back to governance systems.

Continuous audit evidence

Deterministic state transitions

Built-in AI safety controls
What Security Professionals Are Saying.
Latest Updates.
What's happening at Redblock.
Explore our Identity Security Resources.
Deepen your understanding of how AI-driven automation and Redblock’s solution for Disconnected Apps across IGA, IAM, PAM, and NHI effectively reduce cybersecurity threats—through expert-crafted whitepapers, datasheets, videos, and case studies.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

Datasheet
Redblock's ROI
Redblock reduces risk by extending Identity governance to more apps and using AI to automate critical security actions in seconds.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

Datasheet
SailPoint + Redblock: Onboard apps in days and seal governance gaps before they become risks
Redblock unlocks SailPoint’s power across the enterprise application stack, eliminating the need for months of custom integrations.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.
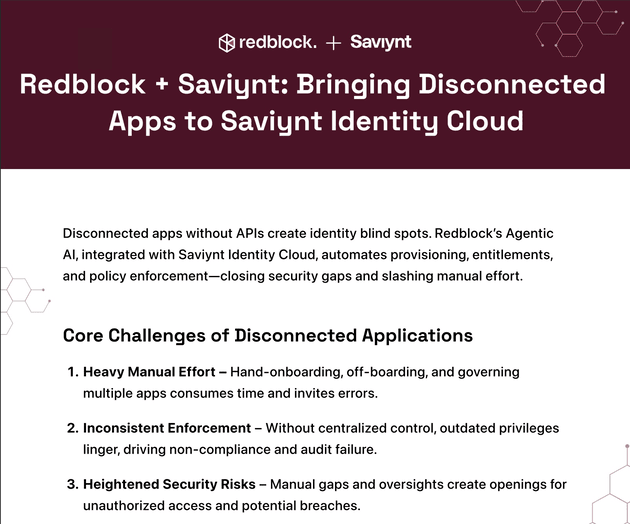
Datasheet
Redblock + Saviynt: Bringing Disconnected apps to Saviynt Identity Cloud
Learn how Redblock's Agentic AI Connector brings Disconnected Apps to Saviynt Identity Cloud.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

This is some text inside of a div block.
Heading
This is some text inside of a div block.

Datasheet
Identity Security for Disconnected Apps
Redblock automates onboarding and off-boarding of users, modification of entitlements, and governance of user access.
Built with the Support of Industry Leaders
We are proud to be backed by visionary investors and partners who believe in our mission to revolutionize cybersecurity.



Close Your IAM Blast Radius.
See how Redblock replaces ticket-driven identity execution with continuous lifecycle enforcement across your application estate.
Book a Demo